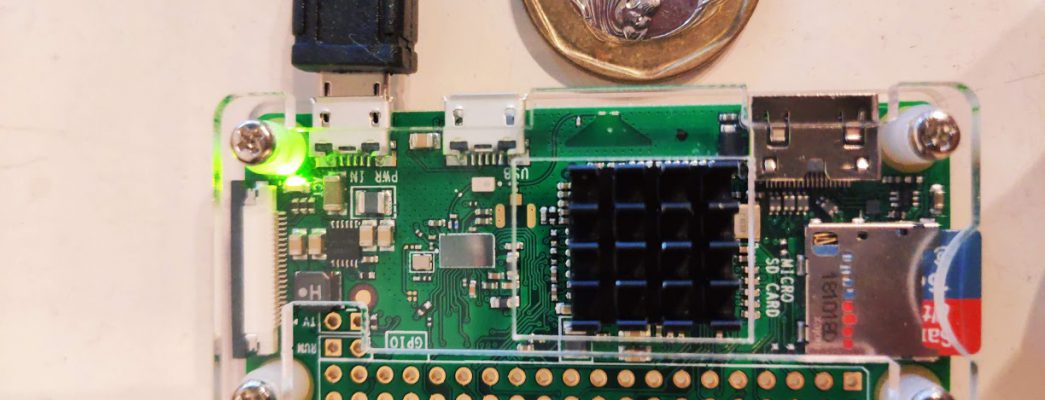
After testing out Pi-hole using containers in Part 1, it is time to deploy it on a more permanent solution so that it can run constantly to protect my entire home network. As the name suggests, Pi-hole is designed to run on Raspberry Pi, and the first step will be to acquire the hardware needed. […]
MY PI-HOLE PROJECT – PART 2 DEPLOY USING RASPBERRY PI ZERO